At WP Provider, we take the security of our websites very seriously.
Therefore, we have taken a number of steps to ensure security, including:
- Perform regular updates to the core and plugins.
- Use of advanced security measures to protect our hosting infrastructure, such as firewalls, malware scanners and other security tools.
- Offer SSL certificates to encrypt communications between the website and visitors and prevent data from being intercepted by unauthorized users.
- Provide regular security updates to ensure that our hosting infrastructure is always up-to-date with the latest security measures and technologies.
- Provide professional assistance to clients who need help improving the security of their website or have questions about security.
- Using duplicate backups to ensure that all our data is always safe and can be easily restored in case of a problem.
In summary, we do everything in our power to ensure the security of our customer websites.
If you need help improving the security of your website or have any questions about security, please do not hesitate to contact us.
We are always ready to help.
Below we technically elaborate on some of the measures we take to improve security.
Modsecurity
ModSecurity is an open source Web application firewall (WAF) used to protect Web applications from various types of cyber attacks, such as SQL injections, cross-site scripting (XSS) and server attacks.
This makes it an important tool for managed WordPress hosting, as WordPress is a popular content management system (CMS) and is therefore often targeted by cyber attacks.
ModSecurity works by filtering incoming HTTP requests to a Web application and detecting potentially malicious requests.
If ModSecurity detects a suspicious request, it can block or reject it, depending on how it is configured.
ModSecurity uses several techniques to detect suspicious requests, including:
- Regular expressions: ModSecurity can use regular expressions (regex) to detect certain patterns in requests.
For example, this can be used to detect SQL injections by looking for specific characters or words typically used in these types of attacks.
- Switching words: ModSecurity may also have a list of switch words or phrases that are considered suspicious activity.
If a request contains any of these switch words, ModSecurity may block or reject the request. - Fingerprints: ModSecurity can also use fingerprints to detect specific attacks.
A fingerprint is a unique combination of characteristics characteristic of a particular type of attack.
If ModSecurity detects a fingerprint in a request, it can block or reject that request.
ModSecurity can also be configured to take certain actions if a suspicious request is detected.
This could include blocking or rejecting the request, as well as generating an alert or maintaining a log file for future use.
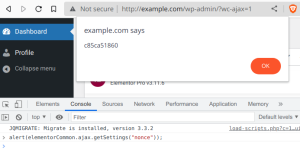
It is important to emphasize that ModSecurity is not perfect and can sometimes generate false positives, meaning that it sometimes blocks or rejects requests that cannot harm the Web application.
Therefore, it is important to properly configure and test ModSecurity to ensure that it achieves its intended goals.
One of the main reasons why ModSecurity is important for managed WordPress hosting is that it helps improve website security.
When a website is attacked, it can lead to data loss, the website becoming unusable and even the server being broken into.
By using ModSecurity, such attacks can be prevented or mitigated, which can lead to less downtime and improved overall website security.
In addition, ModSecurity can also help improve website performance.
When a Web site is under attack, it can lead to slow load times and a worse user experience.
By using ModSecurity, these attacks can be blocked, which can lead to faster load times and a better user experience.
Finally, it is also important to emphasize that ModSecurity is frequently updated to ensure that it is up-to-date with the latest security measures and technologies.
This means that website owners who use ModSecurity can always count on the best possible security for their website.
ConfigServer eXploit Scanner
cxs (ConfigServer eXploit Scanner) is an open source tool for scanning systems for malware and other security problems.
It is designed to work on Linux systems and can be used to scan both files and memory for malware.
cxs works by using a list of fingerprints of known malware to search for known malware on the system.
If cxs detects a fingerprint of malware, it can remove it or issue a warning, depending on how it is configured.
In addition, cxs can also be used to scan the system for security problems, such as improperly configured file access rights or insecure system configurations.
If cxs detects a security problem, it can report it or resolve it automatically, depending on how it is configured.
cxs can be used in conjunction with other security tools, such as ModSecurity, to enhance a system’s security.
It can also be used to regularly scan systems to ensure they are free of malware and security problems.
ConfigServer Firewall
CSF (ConfigServer Firewall) is an open source firewall for Linux systems designed to protect systems from security problems such as malware, brute force attacks and other forms of cyber attacks.
CSF works by filtering incoming and outgoing traffic on a system and blocking or allowing traffic based on predefined rules.
These rules can be based on various factors, such as IP address, port number, protocol and other characteristics of the traffic.
If CSF detects traffic that does not meet the defined rules, it can block or reject that traffic.
As a WordPress hosting user, you can use CSF to improve the security of your hosting environment.
For example, CSF can be used to prevent unwanted traffic from entering your system, such as malware or brute force attacks.
In addition, CSF can also be used to prevent your system from sending traffic to unsafe locations, such as phishing websites or malware distribution points.
CSF is a powerful tool to enhance the security of your hosting environment and can help prevent your system from being targeted by cyber attacks.
However, it is important to stress that CSF is not perfect and it is always important to take measures to strengthen your system’s security, such as using strong passwords and keeping regular updates.
Active monitoring
WP Provider is a hosting provider that focuses on providing high-quality managed WordPress hosting.
One of the most important aspects of WP Provider’s services is hosting infrastructure monitoring and security.
WP Provider continuously monitors the performance of its hosting infrastructure to ensure that client websites are always fast and reliable.
This includes monitoring the servers, networks and other parts of the infrastructure to detect if there are any problems.
If problems are detected, they are fixed immediately to ensure that clients’ websites are always performing well.
In addition, WP Provider also monitors the security of the hosting infrastructure to ensure that it is free of malware and other security issues.
This includes using tools such as ModSecurity and cxs to scan for malware and other security issues.
If security issues are detected, they are fixed immediately to ensure that the hosting infrastructure is always secure.
WP Provider also provides regular security updates to ensure that the hosting infrastructure is always up-to-date with the latest security measures and technologies.
This helps to ensure that the hosting infrastructure is as protected as possible against cyber attacks.
In summary, WP Provider continuously monitors the performance and security of its hosting infrastructure to ensure that clients’ websites are fast and reliable and to prevent the hosting infrastructure from being targeted by cyber attacks.
This makes WP Provider an attractive choice for those looking for high-quality managed WordPress hosting with a high level of security and performance.
Duplicate backups
With us, duplicate backups are used to ensure that all our data is always safe and can be easily restored in case of a problem.
Among other things, we use two additional different backup tools besides the standard backups: Veeam and Borg Backup.
Veeam is a professional backup tool designed to create fast and efficient backups of virtual machines and physical servers.
With Veeam, we can easily create complete snapshots of our servers and store them in various off-site locations.
This gives us assurance that we always have a recent backup that we can use to restore our servers if there is a problem.
Borg Backup is an open source de-backup tool designed to easily and efficiently back up individual files and folders.
Borg Backup uses a combination of encryption and compression to secure the files in the archive.
When a file is added to the archive, it is compressed to reduce the amount of space it takes up.
Next, the file is encrypted using a user-defined key to ensure that it is unreadable to unauthorized users.
By using different tools and locations for backups, we have a double layer of protection to protect our data.
If there is a problem with our servers, we can fall back on the Veeam backups to restore our servers.
If there is a problem with individual files, we can fall back on the Borg backups to restore them.
This gives us peace of mind that we can always fall back on a recent backup if there is a problem, which helps ensure that our data is always safe.
Updates & Patches
At WP Provider, we take the security of our clients websites very seriously, which is why we regularly perform core and plugin updates.
These updates are designed to improve website security and ensure that the websites are always up-to-date with the latest features and technologies.
When we perform core updates, we update the WordPress software itself, including the CMS (Content Management System) and other parts of the system.
These updates often include security enhancements that protect the website from cyber attacks and other security issues.
It is important to emphasize that core updates are essential to the security of a website and it is not advisable to skip these updates.
In addition, we also perform regular plugin updates.
Plugins are pieces of software that can be added to the WordPress website to provide additional features.
As with any software, plugins may contain security issues or may be outdated by newer versions.
Therefore, it is important to ensure that all plugins on the website are up-to-date and that they are updated regularly.
By performing regular core and plugin updates, we ensure that our clients’ websites are always secure and up-to-date with the latest features and technologies.
We understand that sometimes it can be difficult to make time for updates, but it is important to emphasize that these updates are essential to the security and functioning of a website.
If you need help with updates or have any questions about the security of your website, please do not hesitate to get in touch.